Microsoft Cybersecurity Architecture
Den här kursen bygger en grund av bakgrundsfakta och insikter för att designa och utvärdera strategier för cybersäkerhet inom följande områden: Nollförtroende (Zero Trust), Governance Risk Compliance (GRC), säkerhetsoperationer (SecOps) samt data och applikationer.
Om utbildningen
Som deltagare lära du dig också hur du utformar lösningar med hjälp av nollförtroendeprinciper och specificerar säkerhetskrav för molninfrastruktur i olika tjänstemodeller (SaaS, PaaS, IaaS).
Målgrupp och förkunskaper
Kursen är utformad för proffessionell IT-personal med avancerad erfarenhet och kunskap inom ett brett spektrum av säkerhetsteknikområden, inklusive identitet och åtkomst, plattformsskydd, säkerhetsoperationer, säkra data och säkra applikationer. Du bör även ha erfarenhet av hybrid- och molnimplementationer.
För att alltid hålla en hög kvalitet på våra teknikkurser använder vi både engelsk- och svensktalande experter som kursledare.
Security, Compliance and Identity
Kursen ingår i programmet Microsoft Security, Compliance and Identity (SCI), kurser och certifieringar inom säkerhet, regelefterlevnad och identitetshantering baserat på Microsoft-teknologier.
Detaljerad information
Kursmaterialet är på engelska, med detta innehåll:
Design solutions that align with security best practices and priorities
Explore Zero Trust and best-practice frameworks. Map designs to Microsoft’s Cloud Adoption Framework and Well-Architected Framework, align with the Microsoft Cybersecurity Reference Architecture and the cloud security benchmark, and build resilience to ransomware and other common threats.
Design security operations, identity, and compliance capabilities
Define regulatory controls and translate them into technical guardrails. Architect identity and access management, enforce least privilege and secure privileged access, and design SecOps capabilities—logging, SIEM/SOAR, detections, and incident response playbooks—for continuous defense.
Design security solutions for applications and data
Protect Microsoft 365 tenants, secure application architectures, and safeguard organizational data with classification, DLP, encryption, and key management. Balance developer velocity with security-by-design patterns and integrate monitoring to prevent data exfiltration.
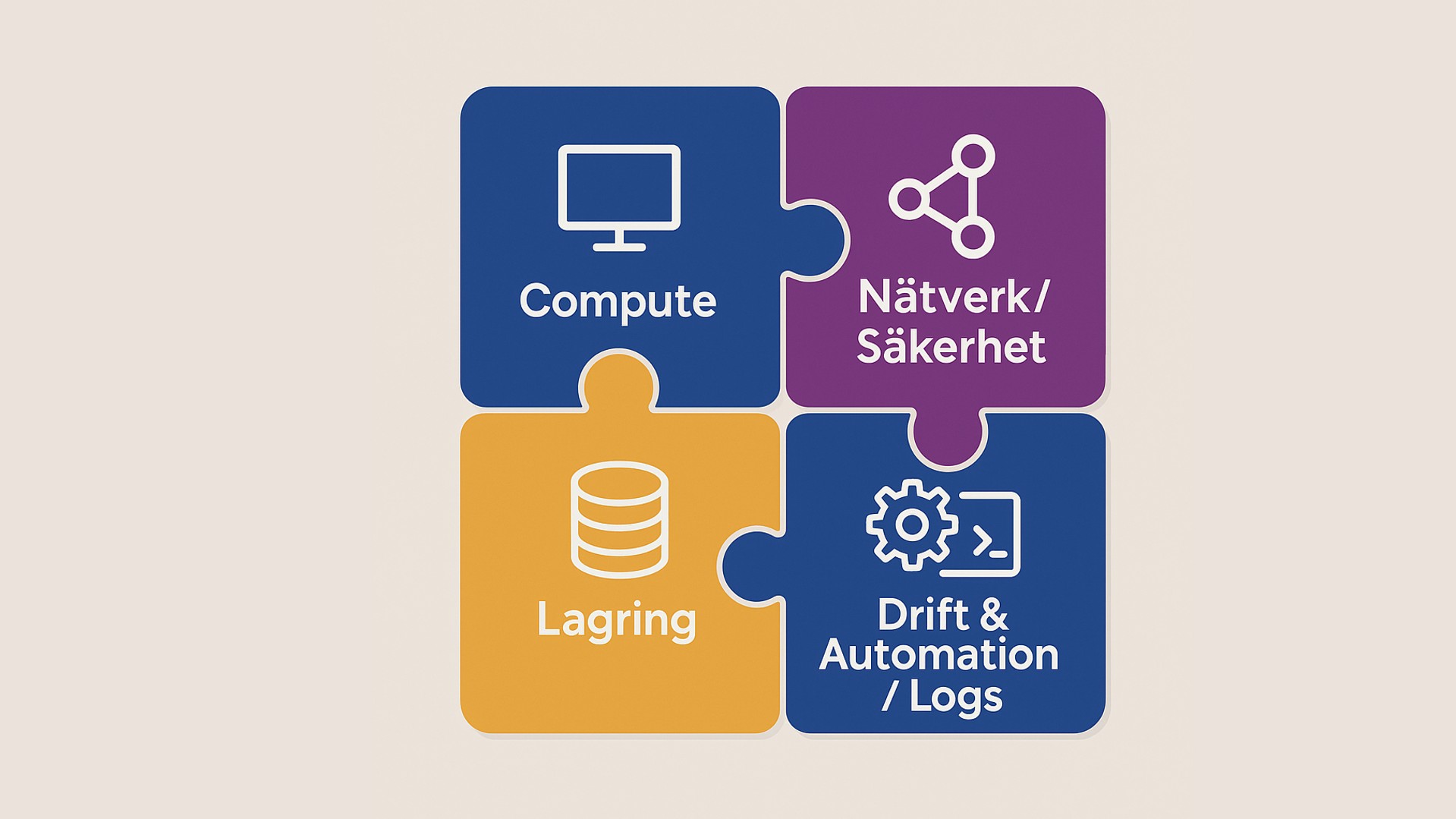
Design security solutions for infrastructure
Specify security requirements across SaaS, PaaS, and IaaS. Establish posture management for hybrid and multicloud estates, harden servers and clients with EDR and baselines, and evaluate network security options—including Zero Trust networking and Security Service Edge—to protect access paths.
Relaterade kurser
Microsoft 365 – Implementing Zero Trust with Conditional Access and MFA
Microsoft Purview - Protect Sensitive Information in the AI Era
Microsoft 365 - Mastering Security, Compliance and Governance
Microsoft Security, Compliance, and Identity - Fundamentals Introduction
Microsoft Defender for Cloud - Extended Securing Azure Services and Workloads
Mer än en kurs
Tre månader som förändrar hur er ledning fattar beslut om AI. Sju sessioner, tolv veckor. Byggt för dem som bär det övergripande ansvaret, inte för dem som ska lära sig verktygen.
Vilken kompetens behöver ni om två år — och har ni den idag? Vi hjälper er planera för framtidens kompetensbehov innan luckorna blir ett problem.
Vet ni vilka kompetensgap som finns i er organisation idag? Vi hjälper er kartlägga nuläget och identifiera vad ni behöver bygga för att möta morgondagens krav.
Ladda kortet med utbildningsdagar i förväg och säkra budgeten innan behovet uppstår. Ni får rabatterade priser, flexibel användning och enklare administration — för hela teamet.
Relaterat innehåll