Utbildningar
Vi har hjälpt människor och organisationer att växa sedan 1993. Oavsett om ni vill stärka teknisk förmåga, utveckla ledarskapet eller effektivisera arbetssättet hittar ni rätt utbildning här.
Utforska efter område
Våra utbildningar inom AI hjälper organisationer att förstå och tillämpa artificiell intelligens, från strategiska beslut till praktisk användning i vardagen.
Inom IT-infrastruktur hittar ni utbildningar inom moln, nätverk, virtualisering och klienthantering från ledande leverantörer som Microsoft, Cisco och VMware.
Inom systemutveckling erbjuder vi utbildningar för utvecklare och tekniska roller inom programmeringsspråk, arkitektur, krav och test samt AI-driven utveckling.
Inom cybersäkerhet hittar ni utbildningar som stärker er organisations förmåga att identifiera, hantera och förebygga de hot som riktas mot era system och er data.
Inom data och analys erbjuder vi utbildningar inom databashantering, visualisering och analysverktyg från ledande plattformar som Microsoft, Oracle och AWS.
Inom ITIL och ramverk hittar ni utbildningar inom IT-servicehantering, DevOps och regulatoriska krav som hjälper er att leverera IT med struktur och kvalitet.
Inom ledarskap och team erbjuder vi utbildningar för alla i organisationen som vill utvecklas inom ledarskap, självledarskap, kommunikation och samarbete.
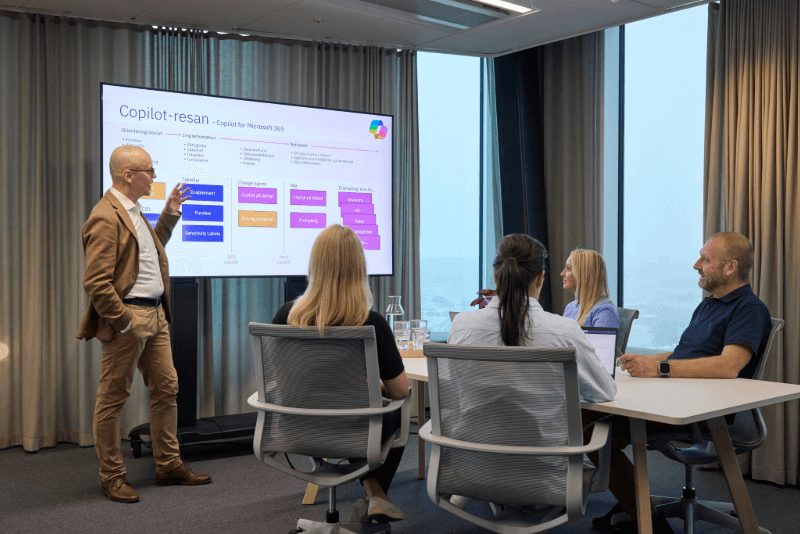
Inom Office och kontorsprogram hittar ni utbildningar som hjälper medarbetare att arbeta smartare i vardagen. Från Microsoft 365 och Copilot till Adobe – med fokus på effektivitet och samarbete.
Inom projektarbete erbjuder vi utbildningar inom projektledning, agila metoder och etablerade ramverk som SAFe, Scrum och PRINCE2 för alla som driver eller deltar i projekt.
Våra utbildningsområden
För alla som vill stärka sin förmåga att arbeta effektivt med digitala verktyg, med fokus på Microsoft 365, samarbete och AI.
För chefer, ledare och IT-ansvariga som vill stärka förmågan att leda människor, projekt och IT-verksamhet med struktur och riktning.
För tekniker och utvecklare som vill fördjupa sin kompetens inom systemutveckling, infrastruktur, cybersäkerhet, data och AI.
Oavsett om du vill bredda din kompetens, certifiera dig eller fördjupa dina kunskaper inom ett specifikt område har vi kurserna för dig.
Executive AI Leadership Program
Ledningsgruppen vet att AI förändrar allt. Men ingen äger frågan. Det här programmet bygger ett gemensamt ramverk, ett gemensamt språk och en delad förmåga att bedöma och prioritera AI-initiativ.
Vad ni får: Gemensamt språk • Bedömningsförmåga • Konkret handlingsplan • Stöd från internationella experter • Nätverkstillgång
Format: 7 sessioner under 12 veckor (3 fysiska halvdagar + 4 digitala)
Läs mer om programmetKompetenskort
Säkerställ bästa tänkbara ekonomiska lösning och att ni har budget när utbildningsbehovet kommer, via Cornerstones kompetenskort. Kompetenskortet laddar ni med ett antal utbildningsdagar vilket ger flexibilitet såväl som bra priser och enkelhet i administrationen.
Vad passar dig bäst?
Relaterat innehåll

